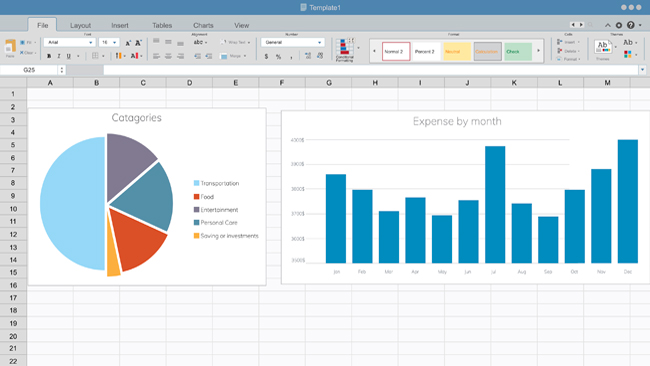
The month-end close process is a critical aspect of financial management for organizations. ..
10 AI Tools for Enhancing Learning and Personal Development
Artificial Intelligence or AI has many interesting applications that tech enthusiasts are ..
Beginners Guide on Understanding Skins Trade
It is no secret that Internet trading can often be challenging to navigate. Knowing whom to trust ..
How to Track a Cell Phone Location Without Installing Software
From ensuring the safety of loved ones to recovering lost devices, it’s useful to know how to track ..
How Studying Grammar Improves Code Readability
As developers and engineers, we are constantly striving to write clean and readable code. Code ..
The Benefits of Decentralized Trading on a Cross-Chain DEX
Decentralized finance (DeFi) has been at the forefront of the blockchain revolution, offering ..
5 Common Access Management Mistakes and How to Avoid Them
Access management is a vital part of maintaining the security of an organization and its systems. ..
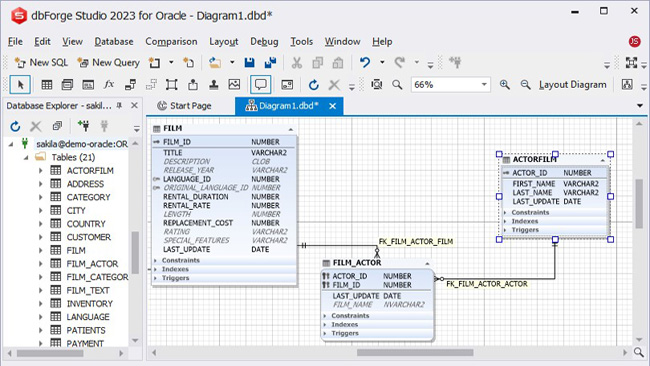
Finding the Best Tool for Oracle Database Design
Navigating the labyrinth of data management in today's digital landscape demands robust and ..
3 Ways Mobile Technologies Are Improving Patient Outcomes
Recent advancements in technology have significantly expanded healthcare. Mobile technology can not ..
Virtual Server for Development and Testing
Welcome to the world of virtual servers, where developers and testers have found a cost-effective, ..
5 Ways Data Entry Outsourcing Can Help Your Business Meet Turnaround Times
It is amazing to see how the business environment is changing at a rapid pace. New technologies are ..
Blockchain Technology And Its Role In Shaping The Future Of Supply Chain Management
Supply chain management is one area that blockchain could yet again revolutionize. The decentralized ..
Natus Vincere: A Dominant Force in the World of CS:GO
Global Reach of CS:GOOne of the most intriguing characteristic of the CS:GO user base is the ..
Different Ways to Control Bitcoin Volatility
Bitcoin became available in 2009 when it was introduced by a pseudo-anonymous name- Satoshi ..
Cell Phone Tracking and Teenagers: How to Balance Trust and Safety
As parents, our primary concern is the safety of our children. With the proliferation of cell ..