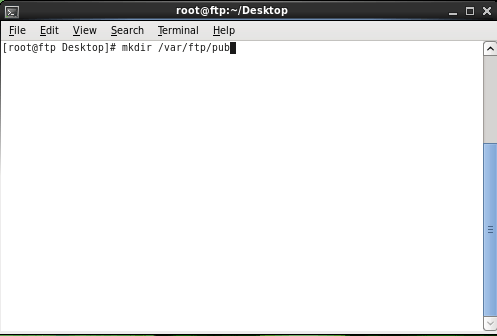
Today, we will show you how to create a repository in Linux. We know that we can install ..
4G Wireless Broadband Breaking into Markets Competitively
Wireless broadband technology 4G is in the news. It is the natural successor to the 3G and 2G ..
5 Reasons Your Mac Needs Antivirus Protection
We all know that person: The smug owner of a Mac, who claims superiority over his or her PC-owning ..
How SMS Over Internet Works: All About Online SMS Sending
The advent of the internet has led to a new era of technology unity that has brought closer many ..