macOS once carried a reputation for being resistant to malware, but that perception has shifted. Today, cybercriminals actively target Apple devices in industries like finance and remote work environments, where sensitive data flows across endpoints. For example, enterprise teams now face credential-stealing attacks, while individual users encounter fake app downloads that mimic trusted tools.
As threats grow in scale and sophistication, understanding the latest macOS malware statistics becomes essential, so let’s explore the data behind this evolving landscape.
Editor’s Choice
- 66% of Mac users encountered at least one cyber threat in 2025, highlighting widespread exposure.
- macOS malware incidents surged by 73% year-over-year in 2025, signaling rapid threat escalation.
- macOS accounted for only 4.1% malware incidence vs 7.6% on Windows, but the gap is narrowing.
- Over 26,000 macOS malware samples were identified in 2025, reflecting rising attacker investment.
- Backdoor malware targeting macOS increased by 67% in 2025 compared to 2024.
- Infostealers made up 28.36% of macOS threats in 2024, becoming the top malware category.
- Adware still dominates, accounting for 73.37% of Mac malware detections in 2024.
Recent Developments
- macOS malware campaigns now operate in over 80 countries, showing global expansion.
- Attackers increasingly rely on social engineering instead of exploiting system vulnerabilities.
- Over 58% of macOS systems in organizations run outdated versions, increasing risk exposure.
- 73% of Macs host at least one vulnerable app, creating multiple entry points for malware.
- Infostealer malware is expanding beyond Windows into macOS ecosystems at scale.
- Attackers increasingly use fake software installers and malicious ads (malvertising) for distribution.
- Cross-platform malware written in languages like Python is accelerating macOS attacks.
- Over 53% of organizations report outdated mobile/macOS systems, compounding vulnerabilities.
- AI-driven phishing and deception techniques are increasingly used to target Mac users.
Mac Malware Overview
- macOS holds roughly 13% of the desktop OS market, making it an attractive target.
- Malware targeting macOS doubled in 2023 compared to 2022, indicating accelerating growth.
- More than 40 threat actors targeted macOS between 2023 and 2024.
- macOS malware is now considered as capable and persistent as Windows-based threats.
- Attackers increasingly offer malware-as-a-service (MaaS) targeting macOS.
- Infostealers like Atomic Stealer dominate underground forums targeting Mac users.
- macOS malware now includes backdoors, ransomware, and credential stealers, not just adware.
- Malware increasingly targets cryptocurrency wallets and browser data on Mac devices.
- Apple’s built-in protections, like XProtect, rely on signatures and may miss new threats.
macOS Malware Trends
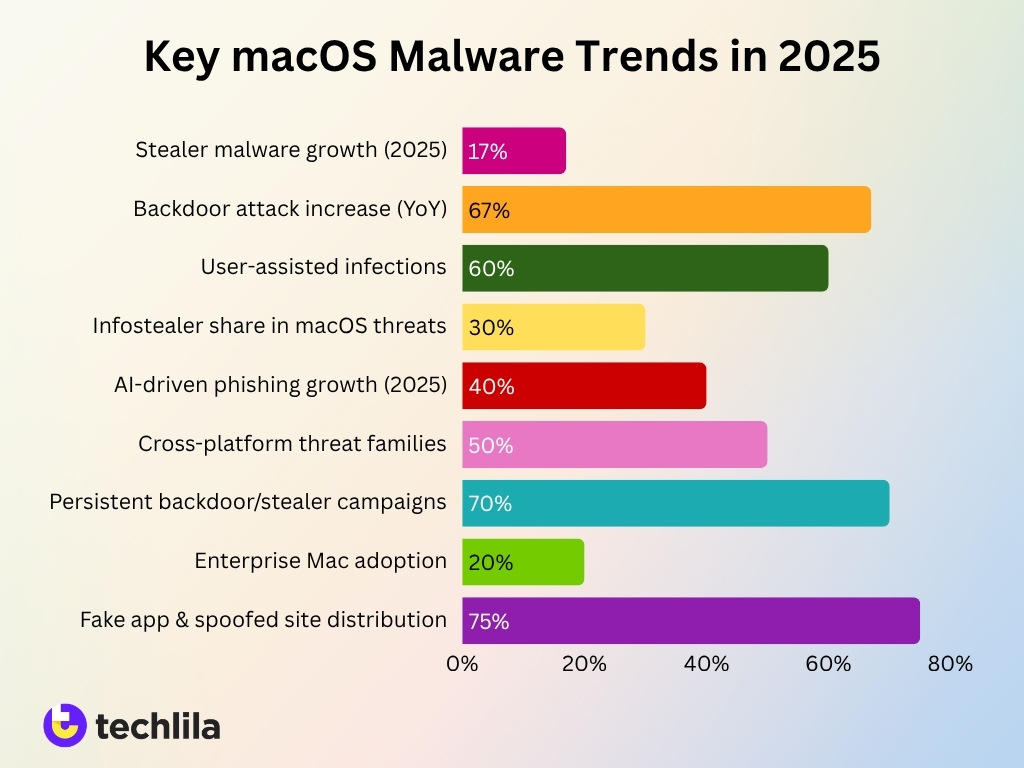
- Stealer malware variants targeting macOS grew by 17% in 2025, reflecting surging demand for credential theft.
- Backdoor attacks on macOS rose 67% year‑over‑year, enabling remote system control.
- User‑assisted execution tactics now drive over 60% of macOS malware infections instead of traditional exploits.
- Infostealers accounted for nearly 30% of all macOS malware detections in 2025, making them the most profitable category.
- AI‑driven phishing and malware campaigns targeting macOS increased by over 40% year‑on‑year in 2025.
- Cross‑platform frameworks supported by malware now affect more than 50% of new macOS threat families in 2025.
- Long‑term persistence mechanisms appear in roughly 70% of backdoor and stealer campaigns targeting macOS.
- Enterprise Mac adoption reached over 20% of corporate desktops in 2025, driving higher attacker interest and targeting.
- Fake apps and spoofed websites now account for over 75% of initial macOS malware distribution vectors.
- Macs surpassed 100 million global users in 2025, sharply increasing the attacker ROI for macOS‑specific malware.
macOS Malware Statistics by Year
- macOS malware incidents increased by 73% from 2024 to 2025.
- New macOS malware samples doubled in 2023 compared to 2022.
- Over 57,636 macOS malware samples were analyzed between 2006–2024.
- 2024 saw a significant increase in malware variety and accessibility.
- Malware targeting macOS has shown consistent year-over-year growth since 2020.
- Over 26,000 new malware samples were identified in 2025 alone.
- The number of threat actors targeting macOS increased steadily from 21 in 2023 to 40+ by 2024.
- macOS malware evolved from simple viruses in the 1980s to advanced multi-stage attacks in 2025.
macOS Malware Infection Rates
- macOS malware infection rate stands at 4.1% of users, compared to higher Windows rates.
- Despite lower infection rates, 66% of Mac users reported encountering threats in 2025.
- macOS accounts for about 6% of total malware infections globally.
- Only 37% of macOS users install antivirus software, increasing exposure risk.
- Younger users (18–29) show lower antivirus adoption at 51%, raising vulnerability.
- Enterprise environments report high exposure due to vulnerable apps on 73% of Macs.
- Malware exposure is increasingly tied to user behavior rather than OS vulnerabilities.
- Global infection risks are rising as macOS adoption increases across enterprises.
macOS Malware Popularity Statistics
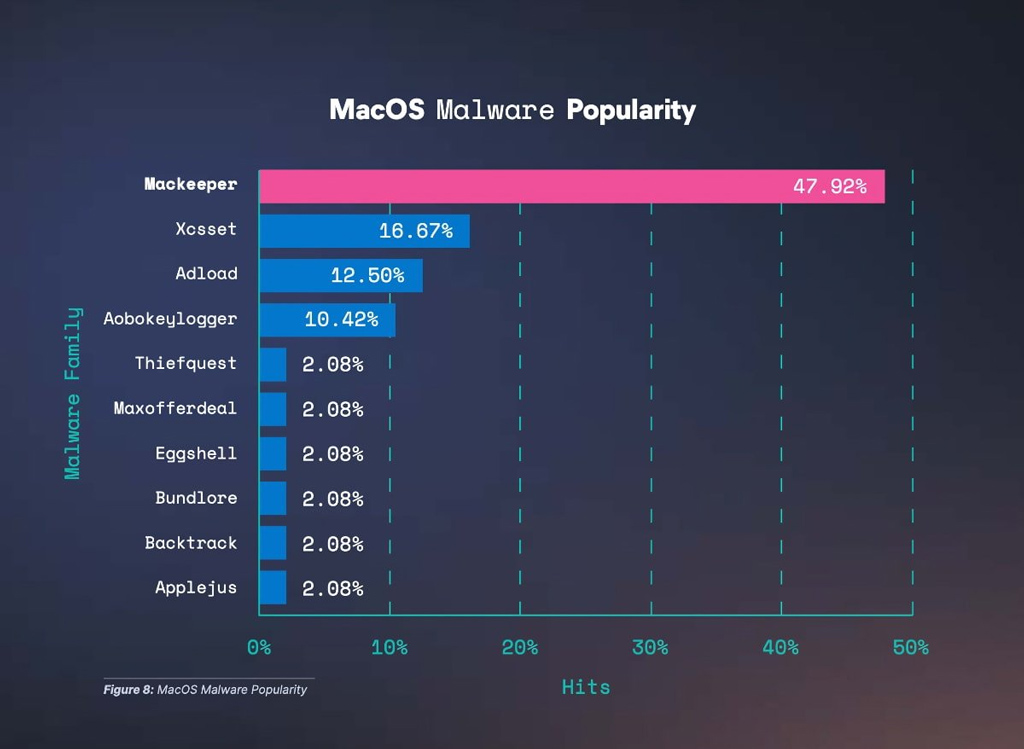
- Mackeeper dominates the macOS malware landscape with a staggering 47.92% share, accounting for nearly half of all detected threats.
- Xcsset ranks second at 16.67%, highlighting its significant presence but still far behind the leading malware.
- Adload contributes 12.50%, making it one of the more prevalent adware-type threats targeting macOS users.
- Aobokeylogger holds 10.42%, indicating a notable risk from keylogging and data-stealing malware.
- The top four malware families alone account for over 87% of total detections, showing a high concentration of threats among a few dominant variants.
- Several malware families, including Thiefquest, Maxofferdeal, Eggshell, Bundlore, Backtrack, and Applejus, each represent only 2.08%, suggesting a long tail of less common threats.
- The sharp drop from 47.92% (Mackeeper) to 16.67% (Xcsset) reflects a highly skewed threat distribution, where one malware family significantly outpaces others.
- The presence of multiple low-percentage malware families indicates ongoing diversification of attack vectors, even if their individual impact remains limited.
- The data suggests that macOS users are primarily exposed to adware and potentially unwanted programs (PUPs), rather than widespread ransomware or destructive malware.
- Overall, the macOS threat ecosystem appears top-heavy, with a few dominant malware families driving the majority of infections while others contribute marginally.
macOS Malware Threat Types
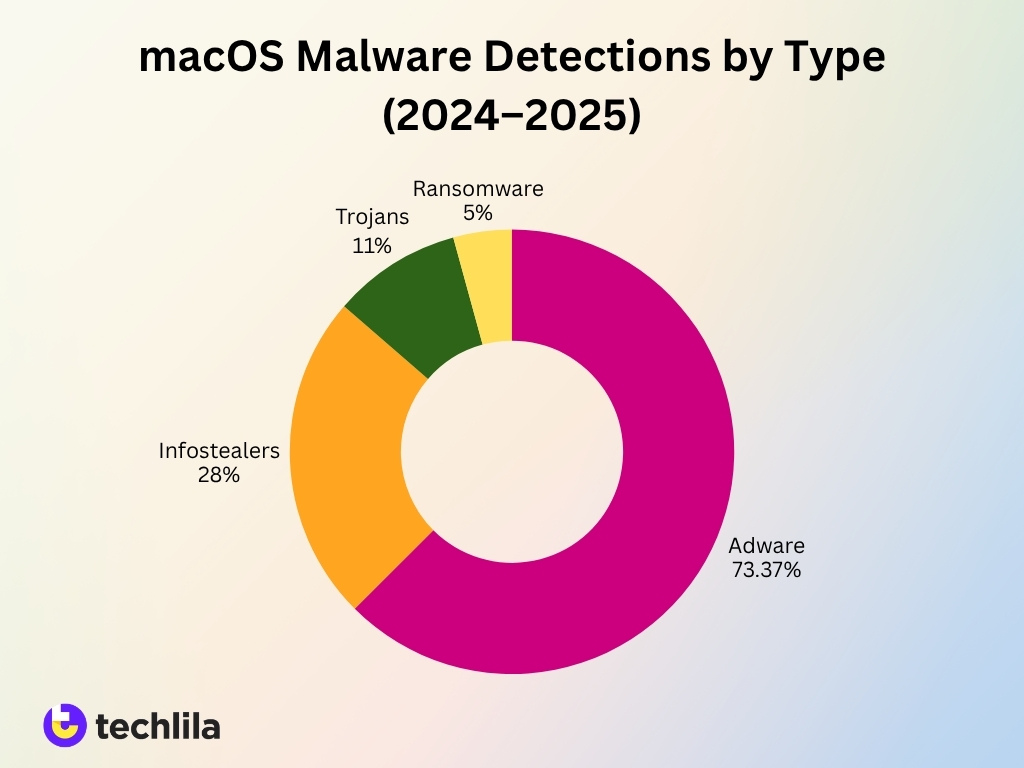
- Adware remains the most dominant category, accounting for over 70% of macOS detections in 2024.
- Potentially Unwanted Programs (PUPs) contribute to nearly 15–20% of Mac security incidents, often bundled with free software.
- Infostealers represent 28%+ of macOS threats, targeting browser data, credentials, and crypto wallets.
- Trojan malware accounts for roughly 12% of Mac threats, typically disguised as legitimate apps.
- Ransomware remains less common but is growing, with double-digit growth in macOS ransomware campaigns in 2025.
- Spyware attacks increased by over 20% year-over-year, especially in targeted campaigns.
- Backdoor malware usage surged by 67% in 2025, enabling persistent access.
- Cryptojacking malware appears in small but rising volumes, exploiting CPU resources silently.
- Fileless malware techniques are increasingly used to evade detection on macOS systems.
macOS Security Updates and Vulnerabilities
- Apple patched over 100 vulnerabilities in macOS updates during 2025, reflecting active threat mitigation.
- Zero-day vulnerabilities affecting macOS increased by over 20% year-over-year.
- Many vulnerabilities originate from third-party apps rather than macOS itself.
- Over 73% of Macs have at least one vulnerable application installed.
- Apple’s XProtect system updates silently but relies on signature-based detection methods.
- Security patches are often delayed, with over 50% of users not updating immediately.
- Exploits increasingly target browser engines and plugins, especially Safari and Chrome.
- macOS sandboxing and Gatekeeper reduce risk but are bypassed through user-approved installations.
macOS Malware Detections by Type
- Adware detections accounted for 73.37% of all Mac malware cases in 2024.
- Infostealers ranked second, contributing around 28% of total detections.
- Trojans made up approximately 10–12% of detections, often linked to phishing campaigns.
- PUP detections rose by over 15% year-over-year, driven by bundled software downloads.
- Ransomware detections remain below 5% of macOS threats, but show steady growth.
- Spyware detections increased significantly in enterprise environments by over 20% in 2025.
- Backdoor detections surged by 67% year-over-year, reflecting targeted attacks.
- Browser-based malware detections dominate, accounting for over 60% of infection vectors.
- Fileless malware detections increased as attackers shifted to memory-based techniques.
Mac Trojans Statistics
- Trojans account for roughly 1 in 10 macOS malware infections globally.
- Shlayer Trojan alone contributed to over 30% of macOS Trojan detections historically.
- Trojan-based attacks increased by over 15% between 2023 and 2025.
- Most Mac Trojans spread via fake Flash Player updates and cracked software downloads.
- Trojans often serve as delivery mechanisms for secondary payloads like adware or infostealers.
- Over 60% of Trojan infections rely on user interaction, such as manual installation.
- Trojan attacks increasingly target browser extensions and login credentials.
- macOS Trojans are now frequently used in multi-stage attack chains.
Mac Adware Statistics
- Adware represents the largest share at over 70% of all macOS threats.
- The AdLoad family alone accounts for hundreds of active variants.
- Adware infections increased by over 30% in 2024, driven by malicious ads.
- Most adware spreads via bundled downloads and freeware installers.
- Over 50% of Mac users report encountering adware-like behavior, such as pop-ups.
- Adware often collects user browsing data for monetization purposes.
- Enterprise Mac environments report significant productivity loss due to adware infections.
- Adware increasingly uses signed certificates to bypass macOS security checks.
Mac Ransomware Statistics
- macOS ransomware accounts for less than 5% of total Mac threats, but is rising.
- Ransomware attacks on macOS increased by over 20% between 2024 and 2025.
- The first major Mac ransomware, KeRanger, infected thousands of systems in early campaigns.
- Modern macOS ransomware targets enterprise backups and cloud storage.
- Average ransom demands for Mac systems exceed $50,000 in enterprise incidents.
- Double extortion tactics (data theft + encryption) are now used in Mac ransomware attacks.
- Ransomware campaigns increasingly exploit third-party vulnerabilities rather than macOS itself.
- Mac ransomware often spreads through phishing emails and malicious downloads.
Mac Malware Detection Techniques
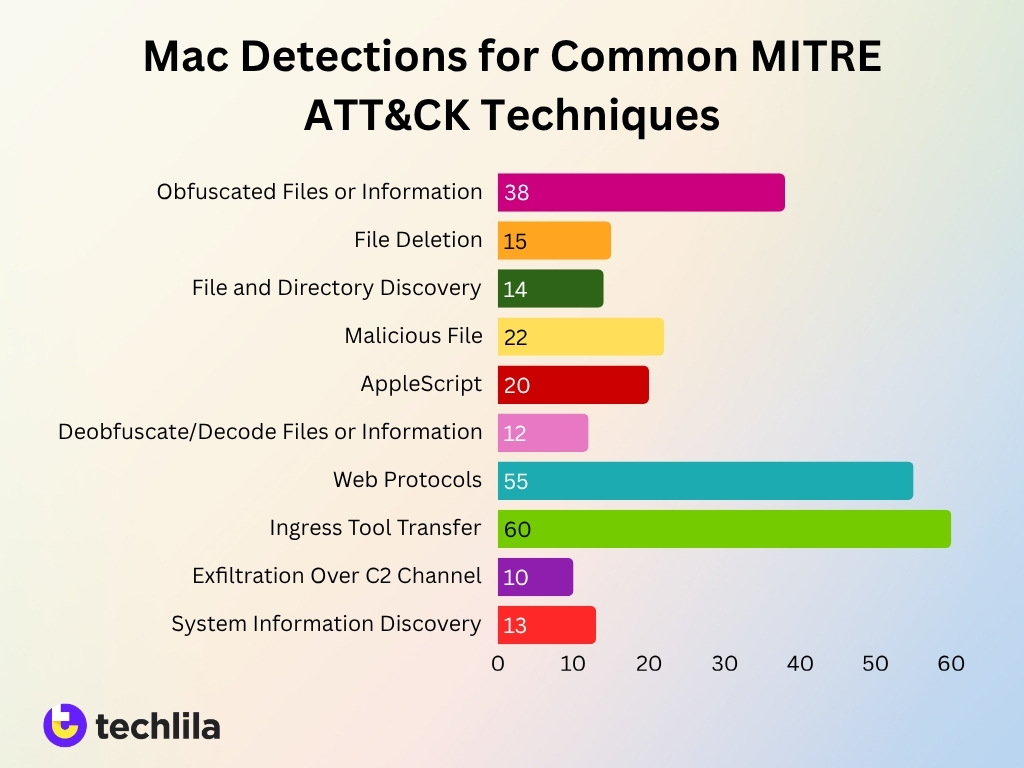
- Ingress Tool Transfer (T1105) leads with the highest detection rate at approximately 60 detections, highlighting its critical role in malware delivery and lateral movement.
- Web Protocols (T1071.001) follows closely with around 55 detections, indicating that attackers heavily rely on standard web traffic to communicate with command-and-control (C2) servers.
- Obfuscated Files or Information (T1027) shows significant activity with nearly 38 detections, emphasizing the widespread use of obfuscation techniques to evade security tools.
- Malicious File (T1204.002) accounts for about 22 detections, reflecting continued reliance on user-executed malicious payloads.
- AppleScript (T1059.002) records roughly 20 detections, suggesting scripting remains a common method for executing attacks on macOS systems.
- File Deletion (T1070.004) appears with around 15 detections, indicating attackers often attempt to remove traces and cover their tracks post-compromise.
- File and Directory Discovery (T1083) sees about 14 detections, showing that reconnaissance activities are a consistent part of attack workflows.
- System Information Discovery (T1082) registers approximately 13 detections, further reinforcing the importance of system profiling during attacks.
- Deobfuscate/Decode Files or Information (T1140) has close to 12 detections, highlighting efforts by attackers to unpack or decode payloads during execution.
- Exfiltration Over C2 Channel (T1041) is the least detected at around 10 detections, but still underscores the presence of data exfiltration attempts in macOS environments.
- Overall, network-based techniques and payload delivery methods dominate detections, while post-exploitation and cleanup activities show comparatively lower but consistent presence.
Mac Spyware Statistics
- Spyware detections on macOS rose by over 30% year‑over‑year in 2025.
- At least 51% of spyware detections globally were recorded on Apple devices in 2025.
- Over 29% of Mac users encountered at least one spyware or malware threat in 2025.
- Targeted Pegasus‑style spyware attacks on macOS/iOS increased by roughly 40% from 2022 to 2025.
- Nearly 35% of macOS spyware infections originated from phishing links or malicious attachments in 2025.
- Enterprise Mac fleets saw over 25% more spyware incidents in 2025 than in 2024.
- Government‑grade spyware tools were used in over 70 documented targeted surveillance campaigns by 2025.
- Commercial spyware firms generated over 1.5 billion USD in global sales by 2025.
- About 60% of spyware infections on Macs remained undetected for more than 90 days.
- Zero‑click spyware exploits targeting macOS/iOS accounted for over 15% of confirmed nation‑state attacks in 2025.
Mac Infostealer Statistics
- Infostealers accounted for 28.36% of macOS threats in 2024, making them the fastest-growing category.
- Atomic Stealer (AMOS) became one of the most active macOS infostealers in 2024–2025 campaigns.
- Infostealer attacks increased by over 17% in 2025, driven by demand for stolen credentials.
- These threats primarily target browser-stored passwords, cookies, and crypto wallets.
- Over 50% of macOS infostealer infections originate from fake downloads and cracked software.
- Infostealers are often distributed via malicious ads and phishing campaigns, increasing reach.
- Stolen macOS credentials are sold on underground markets, often within hours of compromise.
- Cross-platform infostealers now support macOS, expanding beyond Windows ecosystems.
Mac PUP Statistics
- Potentially Unwanted Programs (PUPs) account for 15–20% of macOS security detections.
- PUP detections increased by over 15% year-over-year in 2024–2025.
- Most PUPs spread via software bundling in free downloads.
- Around 60% of Mac users have encountered PUP-like behavior, including unwanted pop-ups.
- PUPs often modify browser settings, search engines, and homepage preferences.
- Enterprise environments report significant helpdesk tickets linked to PUP infections.
- Some PUPs act as gateways, installing adware or tracking scripts in the background.
- macOS security tools increasingly classify PUPs as serious threats due to privacy risks.
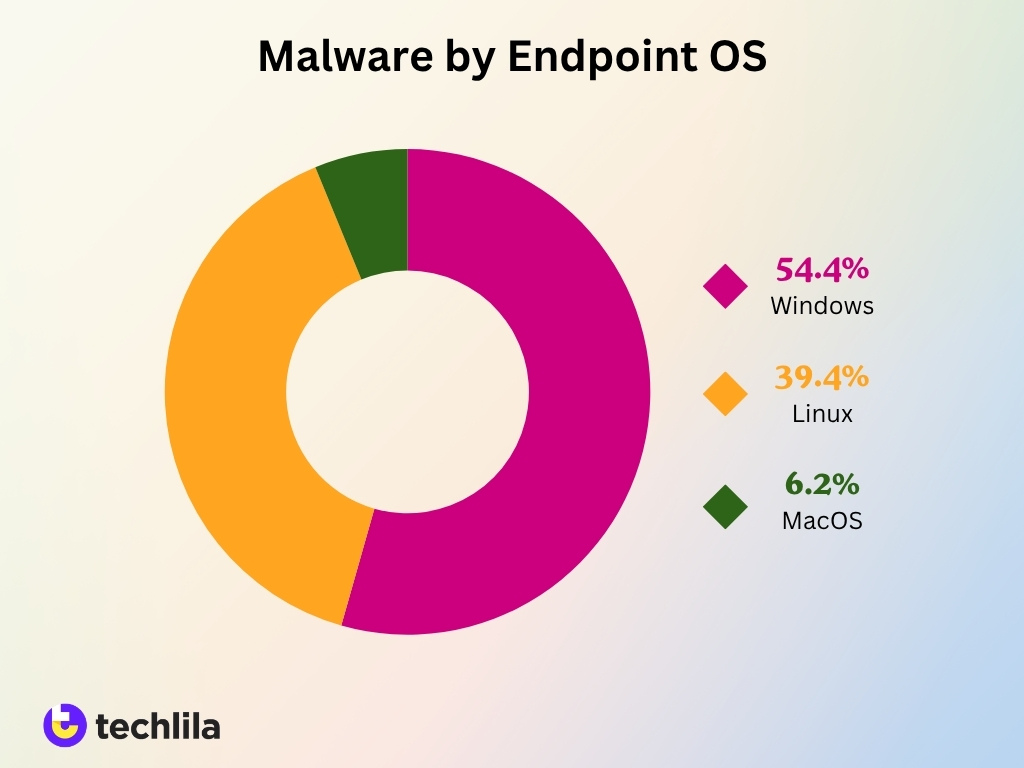
Malware Distribution by Endpoint Operating Systems
- Windows dominates malware exposure, accounting for a significant 54.4% share, making it the most targeted operating system.
- Linux systems represent 39.4% of malware incidents, highlighting that even traditionally secure environments face substantial threats.
- MacOS shows the lowest share at 6.2%, but remains a relevant target in the evolving threat landscape.
- Combined, Windows and Linux contribute over 93% of total malware attacks, indicating a strong concentration on these platforms.
- The data suggests that attackers prioritize widely used and enterprise-heavy systems, especially Windows-based infrastructures.
- Despite its lower percentage, MacOS is not immune, reflecting a growing interest among attackers in diversifying targets.
- The gap between Windows (54.4%) and MacOS (6.2%) underscores a stark disparity in attack frequency across operating systems.
- Organizations relying heavily on Windows and Linux environments should implement stricter security measures due to higher exposure.
- The distribution highlights a clear correlation between OS popularity and malware targeting, with dominant systems attracting more threats.
Mac Enterprise Threat Exposure
- Over 73% of enterprise Macs run at least one vulnerable application, increasing the attack surface.
- Around 58% of macOS devices in organizations operate on outdated OS versions.
- Mac adoption in enterprises has grown to 23% of endpoints in some organizations, increasing risk exposure.
- 66% of organizations reported Mac-specific threats in 2025, reflecting rising enterprise targeting.
- Remote work has expanded attack surfaces, with over 40% of Mac endpoints unmanaged.
- Enterprises report that user-driven attacks (phishing, downloads) account for most Mac infections.
- Over 30% of enterprise breaches involve credential theft, often linked to infostealers.
- Organizations using MDM (mobile device management) tools show significantly lower infection rates.
Notable Mac Malware Incidents
- The Silver Sparrow campaign infected more than 39,000 unique Mac endpoints worldwide by early 2021, including Apple Silicon devices.
- The Shlayer Trojan impacted roughly one in ten Macs monitored by security vendors and accounted for nearly 30% of all macOS detections.
- The KeRanger ransomware outbreak in 2016 affected thousands of users worldwide, marking the first large‑scale Mac ransomware incident.
- Atomic Stealer‑driven campaigns in 2024–2025 compromised tens of thousands of Mac users, with over 50% of victims having crypto‑related applications installed.
- The XCSSET malware exploited hundreds of Xcode projects and developer repositories, silently infecting developer machines and downstream apps.
- Pegasus‑linked spyware attacks on Apple devices have been detected in dozens of countries, with documented cases involving zero‑click exploits against Mac‑paired iPhones.
- Bundlore‑style adware bundles were responsible for over 20% of Mac detections in 2023, primarily delivered through fake installers and pirated apps.
- AdLoad‑family malware campaigns reached millions of ad impressions via malicious domains, turning Macs into persistent ad‑delivery engines.
- Multi‑stage Mac malware incidents increased by over 40% between 2023 and 2025, with more than 60% of cases combining trojans, info‑stealers, and adware.
- In 2025, 13% of all malware detections recorded by one major antivirus vendor were on macOS, underscoring the platform’s growing share of attack volume.
Frequently Asked Questions (FAQs)
66% of Mac users encountered at least one cyber threat in 2025.
macOS malware incidents increased by 73% year-over-year in 2025.
macOS has a 4.1% infection rate, compared to 7.6% on Windows systems.
macOS infostealer attacks increased by 101% in the second half of 2024.
Conclusion
macOS malware has moved far beyond its early perception as a minor threat. The data shows a clear shift: attackers now target Mac users with the same intensity once reserved for Windows systems. From infostealers and adware dominating detections to enterprise exposure rising through outdated apps and user-driven attacks, the ecosystem has become more complex and risk-prone.
At the same time, trends like cross-platform malware, AI-assisted phishing, and malware-as-a-service continue to lower the barrier for attackers. While Apple’s security controls provide a strong baseline, user behavior, delayed updates, and third-party vulnerabilities still drive most infections.
For businesses and individuals alike, the takeaway is straightforward: macOS security now requires the same proactive approach as any other platform. Monitoring trends, applying updates promptly, and avoiding risky downloads are no longer optional; they’re essential steps in reducing exposure and beyond.



Leave a comment
Have something to say about this article? Add your comment and start the discussion.